deepfakes
Scammers cloned a child’s voice using three seconds of audio. The industry calls it 'democratization.'
A forensic post-mortem on the 1,210% surge in AI voice fraud. How 3 seconds of audio and a $5 tool cost a Hong Kong firm $25.6 million.
The marketing copy for generative audio usually follows a predictable rhythm: "unlock your creativity," "scale your content," and the ever-reliable "democratize professional production." However, for Jennifer DeStefano, the democratization arrived in January 2023 as the sound of her 15-year-old daughter sobbing on the other end of a phone call, allegedly kidnapped and held for a $1 million ransom CNN. The voice was perfect—the inflection, the gasping breaths, the specific cadence of a child in terror. It was also entirely synthetic, a "vishing" (voice phishing) attack constructed from a handful of audio snippets harvested from social media.
The rapid commodification of high-fidelity voice synthesis has fundamentally compromised voice-based trust protocols, shifting the burden of security from technical biometrics to manual, analog verification strategies. Analysis of incident logs from 2023 to 2025 reveals that the cost of high-fidelity impersonation has dropped to roughly $5 and three seconds of effort, resulting in a documented 3,000% surge in identity fraud attempts. As we transition from the era of "uncanny valley" robotic stutters to indistinguishable clones, the assumption that a familiar voice belongs to a familiar human has become a dangerous legacy habit. We are currently witnessing a systemic failure of vocal authenticity where the barrier to entry for sophisticated crime has been lowered to the price of a latte.
Incident Summary: The Death of the 'Uncanny Valley'

In the early 2020s, AI-enabled fraud was largely a theoretical threat or a low-resolution curiosity. By early 2025, however, the "uncanny valley"—that psychological safety net where humans instinctively detect "wrongness" in synthetic media—has effectively been paved over. According to data logged by Deepstrike.io, deepfake-enabled deepfake fraud incidents in North America surged by over 1,740% in 2023 compared to the previous quarter. This isn't just a volume problem; it is a quality problem that bypasses the natural skepticism of the human ear.
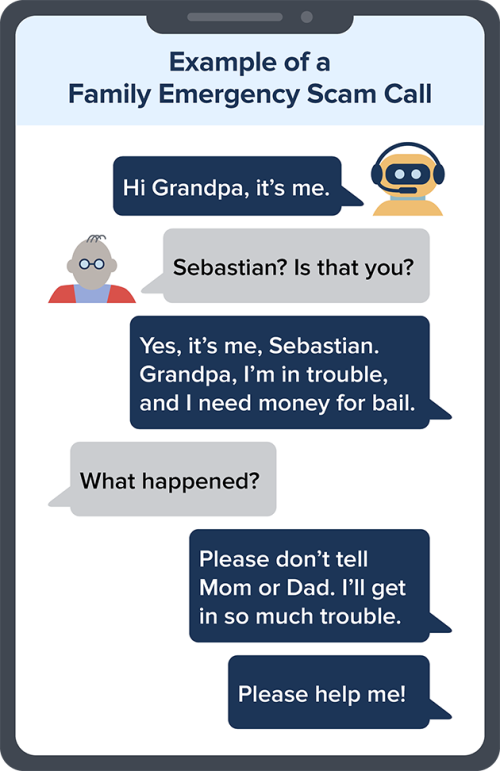
The shift is most visible in the broader category of imposter fraud. The Federal Trade Commission (FTC) documented over 845,000 reported incidents of imposter fraud in 2024 FTC, many of which incorporated AI-generated vocal elements. While older "Grandparent Scams" relied on the victim’s failing hearing or a bad connection to mask a stranger's voice, modern "Synthetic Media" attacks use the actual timbre and emotional micro-expressions of the victim’s family members. The technical ability to replicate "emotional prosody"—the rhythm and pitch that convey feelings—has removed the last detectable fingerprint of the machine.
The terminology matters: Voice Cloning is the specific use of generative adversarial networks (GANs) or diffusion models to replicate a person's vocal profile. Synthetic Media covers the broader output, while Vishing is the delivery mechanism. By 2025, these definitions have blurred as scammers combine cloned voices with real-time translation and emotion-injection modules. The result is a toolkit that allows a non-native speaker in a basement halfway across the world to sound like your spouse having a panic attack.
This surge correlates precisely with the accessibility of tools that require zero technical expertise. In 2019, an AI heist targeting a UK energy firm required enough computing power and audio data to be considered a "sophisticated operation" Wall Street Journal. By 2025, the same result can be achieved using browser-based tools that have bypassed basic safety audits. This has turned what was once a state-actor capability into a commodity for petty scammers who previously lacked the skills to record a voicemail.
Timeline: From Novelty to Commodity

To understand the current crisis, we must look at the receipts. The evolution of voice cloning fraud has moved from high-value corporate targets to mass-market consumer exploitation. Each milestone represents a technical barrier being demolished in favor of "user experience" for the fraudster.
- September 2019: In one of the earliest documented cases of AI vishing, scammers used synthetic audio to impersonate the CEO of a UK-based energy firm, tricking a subordinate into transferring $243,000 to a Hungarian bank account Wall Street Journal.
- April 2023: The Jennifer DeStefano case goes public, marking the shift into "Virtual Kidnapping." DeStefano later testified before the U.S. Senate, noting that the clone captured "the way she would have cried" The Guardian.
- February 2024: The Arup Incident. A Hong Kong-based employee is tricked into transferring HK$200 million ($25.6 million) after a group video call where every other participant—including the UK-based CFO—was a deepfake South China Morning Post.
- January 2025: A March assessment by Consumer Reports reveals that leading voice cloning companies failed 2025 safety audits, demonstrating that the industry's self-regulation is functionally nonexistent Deepstrike.io.
The timeline highlights a terrifying trend: the reduction of the "audio buffet" required for a successful clone. In 2023, models often needed several minutes of clean audio. By early 2025, the industry standard for a baseline clone has plummeted to a mere 3 seconds of original audio—a length easily harvested from a single TikTok or Instagram Reel. This is the Three-Second Threshold, a point where the distinction between a private individual and a public data source evaporates entirely.
Root Cause: The Anatomy of a Three-Second Heist

The collapse of vocal trust is not an accident of the technology; it is a market feature designed for "zero-shot" synthesis. The root cause lies in the shift from concatenative synthesis to neural audio codecs and large language models (LLMs) trained on millions of hours of human speech. Research into models like Microsoft's VALL-E has demonstrated that a model can generalize a person's entire vocal range from a snippet of speech Microsoft Research.
Social media has effectively become a public library for scammers. Anyone with a public profile has likely uploaded enough audio for a high-fidelity clone. This "audio buffet" is then fed into platforms like ElevenLabs, Descript, or PlayHT. While these companies claim to have implemented safeguards, a 2025 audit by Consumer Reports found that 4 out of 6 major providers failed to block unauthorized cloning attempts of private individuals Deepstrike.io. The tools are simply too efficient to be safe.
The commodification is further driven by the lack of Know Your Customer (KYC) verification. For as little as $5, an anonymous user can upload a 3-second clip and generate hours of synthetic speech. The "democratization" of these tools has outpaced the development of "audio watermarking" or detection software, which remains largely reactive and prone to false negatives. Until the cost of generating a clone includes the cost of proving identity, the market will continue to favor the attacker.
Security analysts now recommend families establish a non-digital "safe word" to verify identities during high-stress calls. This is a manual fallback for a failed technical environment. The Safe Word protocol is the only reliable defense left in an era where the FBI's Internet Crime Complaint Center (IC3) continues to log exponential growth in vishing losses FBI IC3 Report. We have officially entered an era where your ears are no longer connected to your brain's security firewall.
The Counter-Argument: Is it the AI or the Panic?

A significant portion of the security community argues that we are over-attributing the success of these scams to the AI itself. Security experts at firms like McAfee have suggested that the heavy lifting in these heists is done by high-stress "panic" tactics—the social engineering of a kidnapping or a corporate emergency—rather than the perfection of the voice clone McAfee. In this view, the AI is merely a "force multiplier" for traditional confidence tricks that have existed for decades.
Defenders of the technology argue that the benefits of "voice accessibility"—allowing those with speech impediments to communicate or dubbing content into multiple languages—outweigh the risks of misuse. They posit that the solution is better public education on social engineering rather than restrictive regulation of generative models. This perspective suggests that the "vocal insolvency" we are seeing is a temporary period of adjustment while humans learn to be more skeptical of their devices.
However, this argument fails to account for the correlation between technical fidelity and success rates. While social engineering is the delivery mechanism, the 1,600% surge in successful attacks directly correlates with the technical ability to bypass the "uncanny valley" response Deepstrike.io. Before 2024, many vishing attempts were thwarted because the victim "heard" something off in the audio. The quality of the synthetic media isn't just a gimmick; it is the key that unlocks the door of human skepticism, turning a low-probability scam into a high-yield heist.
Impact & Fallout: The Erosion of Digital Presence
The financial damage is staggering, with the Arup heist alone accounting for $25.6 million in losses. But the psychological fallout is arguably more corrosive. Virtual kidnapping cases like DeStefano's leave victims with lasting trauma, fundamentally altering how they interact with their own devices. The phone, once a lifeline for families, has become a potential conduit for psychological warfare.
The fallout has reached the banking sector as well. For years, financial institutions pushed "My voice is my password" as a secure biometric login. By mid-2025, many major banks have been forced to quietly abandon these protocols as the failure rates against AI clones reached unacceptable levels. According to Deepstrike.io, the reliability of standard voice biometrics has dropped to less than 40% when tested against current-gen synthetic clones.
| Incident Type | Financial Impact (Avg/Single) | Reported Surge (2024-2025) |
|---|---|---|
| Consumer Vishing | $5,000 - $50,000 | 1,210% |
| Corporate CEO Fraud | $250,000+ | 800% |
| Multinational Deepfake Heist | $25.6 Million | New Category |
The result is a return to analog verification. We are seeing a "Digital Dark Age" of trust where nothing transmitted over a standard telephony or VoIP connection can be confidently attributed to the alleged sender without secondary, out-of-band confirmation. This isn't progress; it's a retreat. The Digital Dark Age is characterized by the systematic devaluation of digital evidence in favor of physical presence and pre-shared secrets.
The Ferrari Defense: Human Intelligence vs. Synthetic Memory
The only consistently successful defense documented in the last twelve months has been human intelligence. In July 2024, scammers targeted a senior executive at Ferrari, using a deepfake of CEO Benedetto Vigna’s voice to request an urgent "confidential acquisition" transfer. The scam allegedly failed when the executive, sensing a slight deviation in the CEO's typical conversational style, asked a personal question: "What was the book you recommended to me recently?" Bloomberg.
The AI, lacking a real-time retrieval-augmented memory of that specific human interaction, could not answer. The executive hung up. This "Ferrari Defense" highlights the obsolescence of technical safeguards. It proves that the only thing a machine cannot clone is a shared history that hasn't been uploaded to the cloud. Cognitive security has replaced technical security as the primary line of defense.
Even OpenAI, the company behind the most advanced LLMs, has notably withheld the public release of its "Voice Engine" tool as of mid-2024, citing "serious risks" related to fraud CNN. This is a tacit admission from the industry’s leader that they cannot build a safe version of this technology in the current environment. When the creators of the tool are too afraid to release it, the "democratization" narrative starts to look more like an apology for an upcoming catastrophe.
Conclusion: The Era of Vocal Insolvency
The evidence from the Arup heist, the DeStefano testimony, and the Consumer Reports safety audits supports the thesis that voice-based trust protocols are effectively dead. The commodification of high-fidelity synthesis has rendered technical biometrics—the very things we were told would replace passwords—useless. We have reached a point where "democratization" has become a euphemism for the dismantling of a fundamental human sensory check.
The 1,210% surge in fraud is not a technical glitch; it is the natural consequence of a market that values speed over safety. Until industry-wide mandatory verification (KYC) is enforced for all cloning tools, and until audio watermarking becomes a hardware-level requirement for telecommunications, the burden of security will remain on the individual. The "Ferrari Defense" and the use of "safe words" are not innovations; they are survival strategies in a landscape that has become vocally insolvent.
Analysis suggests that we are not entering a new era of communication, but rather a period where vocal authenticity is a luxury that requires physical verification. The "Three-Second Threshold" has fundamentally changed the cost of crime, and the current regulatory response is inadequate. If you can’t verify it with a question only the real person can answer, you have to assume it's a $5 clone. The burden of security has officially shifted back to the human, and the machine is no longer our ally in determining what is real.
PRESET: incident-report (Structured post-mortem of a specific AI failure — timeline, root cause, fallout) LANGUAGE: en TARGET WORD COUNT: 1500–2500